SOFTWARE & DIGITAL PLATFORMS(2026 – 2028)

A Decision Briefing for Tier 2 and Tier 3 SaaS & Platform Company Leaders
READ THIS FIRST
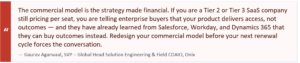
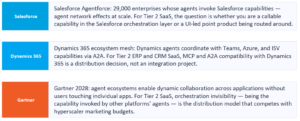
You are a Tier 2 or Tier 3 SaaS or platform company. Your buyers are enterprise or upper-mid-market. Your competitors include Salesforce, Dynamics 365, ServiceNow, and Workday — all of whom restructured their commercial models around outcome units in 2025-2026. You cannot out-invest them on R&D or sales headcount. You can out-think them on commercial architecture, out-govern them on trust infrastructure, and out-execute them on domain-specific intelligence. That is the game this briefing is designed to help you win.
This is a decision framework — 36 decisions, organised under 7 meta-forces in the order you should execute them, with evidence from companies already doing each one, metrics to measure your progress, and a quarterly action plan for 2026. Read it like competitive intelligence. Act on it like the strategic briefing it is.
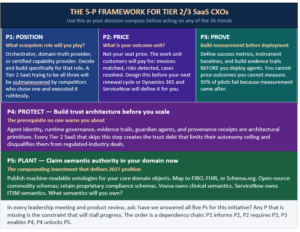
THE 5-P FRAMEWORK — YOUR DECISION COMPASS
Before engaging with any of the 36 trends, answer these five questions. They define your strategic context. If you cannot answer all five clearly, the trends will feel like a list of tasks rather than a coherent transformation strategy.
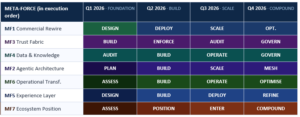
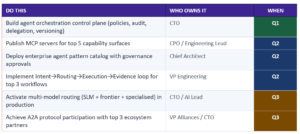
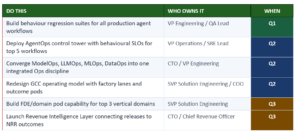
TRANSFORMATION GANTT — WHEN EACH META-FORCE PEAKS
The seven meta-forces do not move in parallel. Each has a quarter when foundational work must complete and a quarter when it compounds. The order reflects the dependency chain: commercial model and trust infrastructure first, because everything else depends on them. Use this as your portfolio view for quarterly planning.
THE 7 META-FORCES IN EXECUTION ORDER

#1 OF 7 · META-FORCE 1 — THE COMMERCIAL REWIRE
How software is bought, priced, sold, and distributed is being structurally rewritten — the winners will be determined by commercial architecture, not feature sets.
You are a Tier 2 or Tier 3 SaaS company. Your buyers have already seen Salesforce’s AELA model, Workday’s Agent Actions, and Dynamics 365 AI Credits — all restructured around outcome units rather than seats. You cannot out-invest these platforms on features or sales headcount. You can out-architect them on commercial design. Seat-based pricing was brilliant when software delivered access. It is structurally broken when software delivers autonomous work. Your commercial model must answer the thesis that Salesforce, Dynamics 365, and Workday have already answered for your buyers — with equal clarity and with a Tier 2-appropriate execution path.
T01 SAAS DECLINES; SERVICE-AS-SOFTWARE (SAS) EMERGES
↳ Customers pay for operated outcomes, not software access
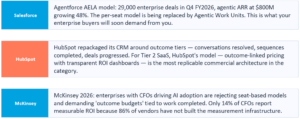
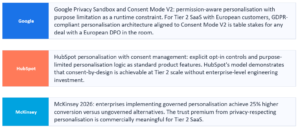
Salesforce closed 29,000 Agentforce deals in one quarter; agentic ARR grew 48% in three months. Pilots without CFO-ready baselines are being cut. Enterprises now evaluate software as an operator: does it complete work reliably, audibly, and with controlled risk? The migration factory — previously a services motion — is becoming a commercial product layer.
WHAT IS CHANGING
- Outcome-backed pilots: CFO-ready proof of cost, throughput, and risk before any scale commitment
- FDIE bundling: Foundation + Deployment + Integration + Enablement as the repeatable service wrapper
- Migration factory as a product motion — recurring revenue tied to work delivered, not installs
- Evidence over demos: measurable time-to-value, failure modes surfaced early, safe-failure handling
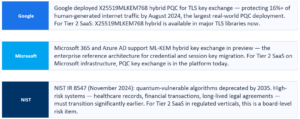
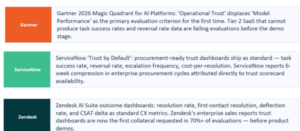
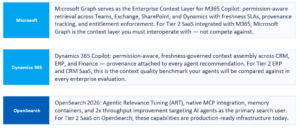
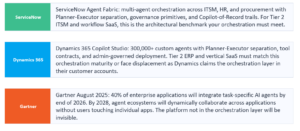
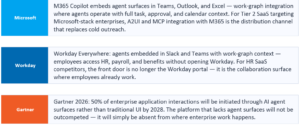
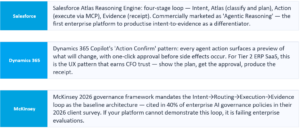
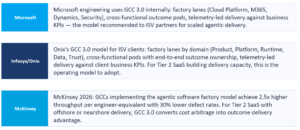
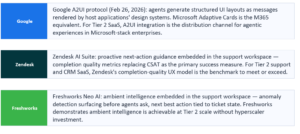
WHO IS ALREADY DOING IT
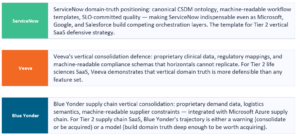
WHAT IT MEANS FOR YOUR BUSINESS
- Revenue aligns to recurring outcome-linked subscriptions instead of one-time installs
- Procurement cycles shorten because finance-ready evidence replaces subjective evaluation
- Lower scale risk as failure modes and controls are engineered upfront, not discovered in production
YOUR ACTIONS
- Redesign the sales motion around work delivered, not seats licensed
- Productize migration and operated delivery into an outcome factory — this is your FDIE wrapper operationalized
- Make trust measurable: evidence trails, reversibility, and escalation design are product requirements
- Ensure every reference customer demonstrates production outcomes, not AI novelty
T02 PRICING REWIRES AROUND WORK UNITS — THE AELA ERA
↳ Seat pricing is commercially misaligned; the AELA model signals where the entire category is heading
Salesforce’s Agentic Enterprise License Agreement — unlimited agentic capacity for long-term commitment — is not a pricing innovation. It is a thesis: accept short-term margin risk for permanent lock-in as the default agentic operating system. Every ISV must decide how to respond. Outcome-based pricing (per resolution, per completion, per verified output) is the structural alternative. The hidden risk: Constellation Research identifies data connection fees as the biggest underestimated cost in scaling AI agents — the new cloud egress charge.
WHAT IS CHANGING
- Outcome-based pricing tied to measurable business results: per resolution, per completion, per verified output
- Agentic Work Units (AWUs): buying a bundle of agent actions per month rather than per seat
- Hybrid models: base subscription plus outcome triggers smooth adoption and revenue predictability
- Performance guarantees and credits when targets are missed — signals alignment and builds procurement trust
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Higher trust and faster procurement when value is provable and aligned to business KPIs
- Premium economics where vendors reliably deliver outcomes
- Lower churn when customers see repeatable results and predictable unit economics
YOUR ACTIONS
- Redefine pricing around outcome units — tickets resolved, claims processed, reconciliations completed
- Instrument outcomes credibly: completion, error, reversal, escalation, and time-to-value
- Map your data toll exposure: which workflows cross vendor boundaries and what does that cost?
- Align sales and customer success compensation to customer KPIs, not usage metrics
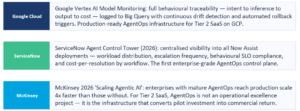
T03 INFERENCE FINOPS AS PRODUCT STRATEGY — THE REVENUE INTELLIGENCE LAYER
↳ Unit economics as first-class product discipline; engineering and revenue in the same data model
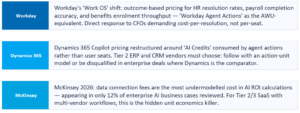
As AI workloads scale, compute and inference costs are no longer marginal. One workflow can swing margin and reliability. Teams that treat FinOps as a finance afterthought will find their outcome pricing models unprofitable the moment they scale. The Revenue Intelligence Layer is the mechanism that fixes this: connect every release and agent version to business outcomes — completion rate, cost-per-resolution, reversals, escalations, and NRR — so engineering decisions are directly tied to revenue outcomes.
WHAT IS CHANGING
- Engineered cost-to-serve: precise resource cost per workflow, per outcome, per tenant
- Dynamic model routing: frontier models only when needed; smaller or specialized models for routine work
- Revenue Intelligence Layer: releases and agent versions linked to completion rate, cost-per-resolution, NRR
- Agentic SDLC cost gates: prompts, tools, and models treated as versioned artifacts because behavior drift is a revenue risk
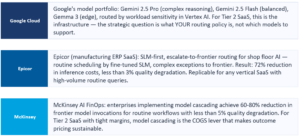
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Margin control through measurable cost-per-outcome and intelligent routing
- Outcome pricing becomes viable because costs per completion are known and managed
- Runaway spend risk drops while maintaining SLA and reliability commitments\
YOUR ACTIONS
- Integrate FinOps into the product runtime: routing, telemetry, and cost dashboards are platform primitives
- Build unit economics views per workflow, per tenant, per agent to optimize for margin, throughput, and reliability together
- Stand up the Revenue Intelligence Layer connecting releases to business outcomes
- Expose economics to customers at the outcome-unit level to reinforce trust and support outcome-based pricing.
T04 HYPERSCALER PARTNERSHIPS SHIFT FROM INFRA DEALS TO OUTCOME GTM
↳ Infra discounts are table stakes; GTM execution and semantic co-ownership are the real partnership assets
Omdia projects hyperscaler marketplace software sales growing from $30B in 2024 to over $160B by 2030. Enterprise cloud spend commitments increasingly fund third-party software purchases. Co-sell motions unlock field scale no ISV can replicate independently. The ISV that treats this relationship as infrastructure optimization is leaving the most valuable asset on the table: distribution, credibility, and procurement-native position.
WHAT IS CHANGING
- Co-sell as default: structured alignment with hyperscaler field teams, pipeline sharing, joint account plays
- Marketplace-first packaging: private offers, enterprise terms, procurement-friendly constructs tied to committed spend
- Joint value propositions: industry plays co-built with hyperscaler architects — not co-branded slides
- Execution automation: deal registration, handoffs, and incentive capture systematized rather than hero-driven
WHO IS ALREADY DOING IT

WHAT IT MEANS FOR YOUR BUSINESS
- Faster pipeline creation by attaching to hyperscaler buying motions
- Shorter sales cycles via marketplace procurement and co-sell credibility
- Higher discoverability across regions and vertical plays; aligned incentives extending your sales force
YOUR ACTIONS
- Make GTM execution the partnership charter — treat infra discounts as baseline
- Package for marketplace procurement: outcome units, private offers, enterprise-ready terms
- Co-build one to two industry value propositions that sell as operated outcomes
- Measure partner impact as revenue: co-sell pipeline, marketplace transactions, partner-sourced bookings
T05 THE SEMANTIC LAYER WARS — WINNING THE PROTOCOL BATTLEGROUND
↳ MCP and A2A solve transport and coordination; they do not solve meaning. The semantic layer is the highest-value uncontested territory in the agentic economy
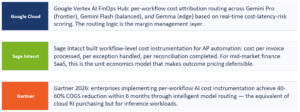
MCP has crossed 97 million monthly SDK downloads. A2A launched with 50+ enterprise partners including Salesforce, SAP, ServiceNow, and Workday. Both are under Linux Foundation governance. But Bain’s analysis identifies the critical gap: neither protocol provides a shared vocabulary defining what ‘invoice,’ ‘approval,’ or ‘patient record’ means. The first ISV to create an industry-wide semantic standard for their domain will earn revenue on every agent transaction in that domain — even when someone else’s agent takes the action.
WHAT IS CHANGING
- MCP as three-layer strategy: connectivity (table stakes), governance (differentiator), semantic authority (moat)
- A2A participation as agent-to-agent coordination standard across organizational boundaries
- Open-source semantic schemas where you already lead — the standards war is active now
- Winner-takes-most dynamics identical to early web: first semantic layer to achieve critical mass wins
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Platforms that own the semantic layer become validation requirements for the entire ecosystem
- ISVs that lead only with UI differentiation become silent back ends as orchestration layers route around them
- Early movers with practical solutions win standards wars — timing is the variable that compounds
YOUR ACTIONS
- Publish production-grade MCP servers for your top five capability surfaces by Q3 2026
- Define your semantic authority layer: what domain objects and business rules does your system define that agents must validate against?
- Participate in vertical standard-setting discussions — open source schemas where you lead, build proprietary constraints where you differentiate
- Instrument MCP surface as a product metric: tool call volume, completion rate, error rate, trust violations
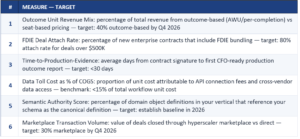
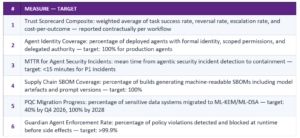
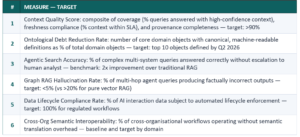
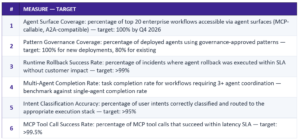
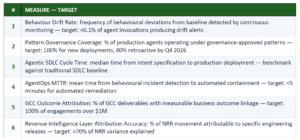
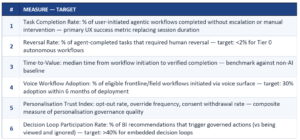
HOW TO MEASURE YOUR PROGRESS — META-FORCE 1: THE COMMERCIAL REWIRE
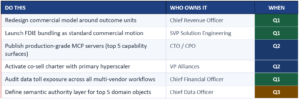
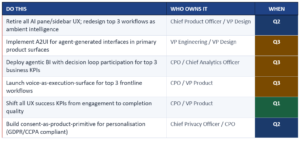
YOUR PRIORITY ACTIONS — META-FORCE 1
#2 OF 7 · META-FORCE 3 — THE TRUST FABRIC
Operational trust, agent identity, runtime governance, AI-native security, supply chain integrity, and quantum-safe cryptography — the six dimensions every enterprise buyer now evaluates before signing.
Every enterprise incident involving an AI agent generates the same investigative question: who authorised this action, under what policy, with what evidence, and can it be reversed? If your platform cannot answer that question within ten minutes from an audit trail, you will lose every regulated-industry enterprise deal you enter — and regulated industries are where Tier 2 SaaS commands premium pricing. The Trust Fabric is not a compliance architecture. It is the commercial infrastructure that allows your agents to operate in the high-value workflows where the largest problems live.
T12 OPERATIONAL TRUST IS THE PROCUREMENT FILTER
↳ Buyers evaluate whether your platform can deliver outcomes with proven task success, predictable cost, safe-failure handling, and evidence-by-default
As agentic systems execute business-critical work, the cost of failure is no longer bad output — it is operational disruption, financial loss, and regulatory exposure. Procurement teams are shifting from ‘does it work?’ to ‘does it operate safely at scale?’ Platforms that cannot prove trust in production are disqualified early. PwC finds 28% of executives cite lack of trust in AI agents among their top three challenges.
WHAT IS CHANGING
- Measurable trust metrics: task success rate, completion rate, error rate, reversal rate, escalation frequency
- Contractual trust frameworks: SLAs, escalation paths, liability boundaries, and performance credits as standard
- Evidence-by-default: every action produces traceable, auditable receipts
- Procurement-ready reporting: dashboards that finance, risk, and IT can read without translation
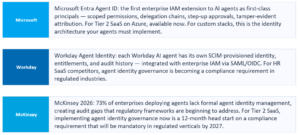
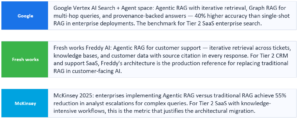
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Shorter procurement cycles because trust evidence replaces subjective evaluation
- Higher adoption and expansion as stakeholders gain confidence in safe execution
- Premium economics for SaS: trust maturity is a differentiator that supports outcome pricing
YOUR ACTIONS
- Make trust measurable: standardize a trust scorecard with success rate, reversals, escalations, and cost-per-outcome
- Productize evidence: receipts and audit trails are default capabilities, not enterprise tier add-ons
- Ship procurement-ready dashboards: CFO, CIO, and compliance packs tied to outcome units
- Tie trust telemetry to the Revenue Intelligence Layer: prove which releases improved or degraded outcomes and margin
T13 AGENT IDENTITY, DELEGATION, AND AUTHORITY — THE NEW IAM PRIMITIVE
↳ Traditional user-based identity cannot govern autonomous workflows; delegation becomes the control mechanism that makes autonomy scalable and compliant
Once agents can approve, change, move, or commit, enterprises need clear answers: who authorized this action, under what policy, with what permissions, and can it be reversed? Traditional IAM was designed for humans logging in. Agentic IAM must handle agents acting on behalf of humans, agents acting on behalf of other agents, and autonomous execution within policy bounds — with a full audit trail at every step.
WHAT IS CHANGING
- Agents as first-class actors: each agent has its own identity, entitlements, and scoped permissions managed through lifecycle
- Delegation and step-up approvals: policy determines when an agent can act, when it must request approval, when it must escalate
- Traceable accountability: every action tied to agent identity, delegated authority, and evidence trail
- Least-privilege by design: agents operate with minimum permissions; high-impact tools require explicit allowlists
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Reduced risk of unauthorized actions through explicit identity and scoped authority
- Higher autonomy where safe: agents execute inside bounded delegation, increasing throughput
- Audit-ready operations: clear attribution accelerates compliance reviews and incident response
YOUR ACTIONS
- Extend identity to agents: treat agents as first-class principals with entitlements and lifecycle management
- Implement delegation policies: explicit rules for autonomy tiers, step-up approvals, and escalation
- Mandate on-behalf-of attribution plus receipts for every consequential action
- Enforce least privilege and tool allowlists at runtime — not in prompts
T14 GUARDIAN AGENTS AND RUNTIME GOVERNANCE
↳ Governance becomes agentic: static policies cannot keep pace with machine-speed execution
Guardian agents monitor, intervene, and enforce policy in real time — at the product level and across the enterprise. The specific risk they address that manual governance cannot: individually compliant agents combining into a non-compliant outcome (collusion-by-composition). When agents coordinate, their combined behavior must also be governed, not just each agent in isolation.
WHAT IS CHANGING
- Real-time policy enforcement: guardians check actions against data classification, consent, approvals, segregation of duties
- Cross-agent risk detection: monitor for emergent patterns where individually compliant agents combine into non-compliant outcomes
- Behavior compliance monitoring: did the system behave within policy under real conditions? — enforced outside the model
- Policy-as-code at runtime: deterministic evaluation that cannot be bypassed by prompt injection or model drift
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Lower governance cost at scale: automation reduces reliance on manual approvals and post-hoc audits
- Reduced catastrophic risk: faster detection of unsafe actions, drift, and cross-agent failures
- Faster deployment cycles: teams ship with confidence when policy is enforced at runtime
YOUR ACTIONS
- Define guardian scope: universal controls versus domain-specific policies for each workflow tier
- Deploy policy-as-code at runtime: guardians interpret, route, and intervene deterministically outside the model
- Monitor cross-agent behavior patterns and treat emergent violations as incidents
- Integrate guardian telemetry into the Revenue Intelligence Layer: quantify how enforcement protects margin and renewals
T15 AI-NATIVE SECURITY ARCHITECTURE — FROM PERIMETER TO AGENT-NATIVE
↳ Prompt injection is an execution risk. Tool misuse is an action risk. Traditional perimeter security has no equivalent for either.
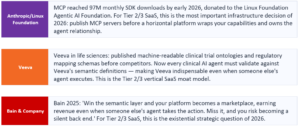
Once agents can take actions, prompt injection becomes an execution risk, not a content risk. Tool use turns APIs, connectors, file systems, and admin actions into reachable surfaces via natural language. When agents pass tasks and context across each other, compromise can propagate laterally unless trust boundaries are explicit. McKinsey identifies five critical risks agents introduce: uncontrolled autonomy, fragmented access, lack of traceability, expanding attack surface, and agent sprawl.
WHAT IS CHANGING
- Runtime validation gates: validate intent, scope, and permissions regardless of model output
- Tool access as primary attack surface: strict allowlists, schemas, step-up approvals, and least privilege
- Multi-agent trust boundaries: identity, scoped tokens, provenance checks, kill-switches prevent lateral movement
- Continuous red-teaming as CI/CD: adversarial testing is a release gate — prompt injection, tool misuse, policy bypass
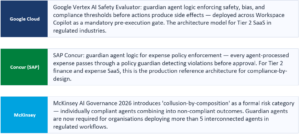
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Lower breach likelihood: deterministic controls reduce blast radius from injection and tool misuse
- Faster incident containment: clear boundaries and traceability improve detection and response
- Safer autonomy at scale: enterprises expand agent execution when enforcement is testable and agent-native
YOUR ACTIONS
- Adopt an agent-native threat model: map tool surfaces, memory stores, context sources, and delegation paths
- Enforce least privilege for agents: scoped credentials per intent, time-bound permissions, explicit allowlists
- Add deterministic runtime gates outside the model: policy engines and action validators
- Run red-team exercises for agents: prompt injection, data exfiltration, unsafe tool chaining, cross-agent movement
T16 SOFTWARE SUPPLY CHAIN SECURITY AND DIGITAL PROVENANCE
↳ In an agentic world, the supply chain expands to models, prompts, tools, and marketplace action extensions — every component must be verifiable, signed, and continuously monitored
Past incidents like Log4Shell and SolarWinds exposed how dependency compromise creates systemic risk. With agents, the blast radius grows: an untrusted component can trigger unauthorized actions, data leakage, or compliance failures. Static checklists will not hold — enterprises will expect continuous, machine-readable governance tied to every build and every agent update.
WHAT IS CHANGING
- Dynamic SBOMs: per build, per agent commit, per model update — continuous and machine-readable
- Signed artifacts and provenance: cryptographic signing for code, containers, model artifacts, and tool extensions
- Compliance-by-design gates: documentation, risk classification, testing evidence required pre-deploy
- Third-party governance for actions: partner and marketplace actions certified, versioned, risk-scored, and revocable
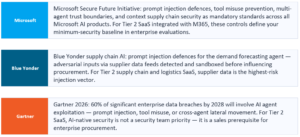
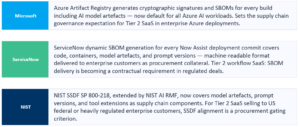
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Reduced surprise vectors through continuous visibility and provenance
- Faster incident response via traceable artifacts and rollback clarity
- Procurement advantage in regulated markets where provenance is a gating requirement
YOUR ACTIONS
- Generate SBOMs continuously: every build, every agent commit, every model push
- Mandate signatures and provenance across code, models, containers, and partner tools — align to NIST SSDF SP 800-218
- Make provenance a platform capability: tamper-evident logs for inputs, intent, context sources, tool calls, and outputs
- Report supply chain posture as an executive KPI: coverage, risk score distribution, remediation cycle time
T17 QUANTUM-SAFE CRYPTOGRAPHY — HARVEST NOW, DECRYPT LATER IS NOT A FUTURE THREAT
↳ Every long-lived secret encrypted today under RSA or ECC is a present liability — the window to act was two years ago
Nation-state adversaries are actively harvesting encrypted data today, with the explicit strategy of decrypting it when quantum computing achieves sufficient scale. NIST finalized post-quantum cryptography standards (ML-KEM, ML-DSA, SLH-DSA) in 2024. For enterprises handling data with multi-year sensitivity — healthcare records, financial transactions, legal agreements — the threat is not hypothetical. The specific agentic amplifier: agent identity credentials, delegation tokens, and execution receipts are cryptographically signed. Compromise these and the entire accountability model for agentic operations collapses.
WHAT IS CHANGING
- Crypto agility: algorithm abstraction enabling algorithm changes via configuration without service interruption
- Hybrid cryptography during transition: classical plus PQC applied simultaneously — if either is broken, the other protects
- Key rotation automation: scheduled, monitored, not manual
- Ecosystem coverage: your crypto agility is only as strong as the weakest partner, SaaS vendor, or MCP connector
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Risk reduction for long-lived data: mitigates retrospective compromise from harvest-now-decrypt-later
- Regulatory confidence: demonstrates proactive security governance to boards and auditors
- Operational resilience: upgrades without downtime protect SaS continuity commitments
YOUR ACTIONS
- Audit quantum exposure today: classify all sensitive data by retention period and regulatory requirement — everything with 5+ years sensitivity is at risk now
- Adopt NIST PQC standards for new sensitive data encryption immediately — the standards are final
- Build crypto agility into the platform: algorithm abstraction, key rotation automation, config-driven transitions
- Apply specifically to agentic identity: agent credentials, delegation tokens, and execution receipts on quantum-safe foundations before fleets scale
HOW TO MEASURE YOUR PROGRESS — META-FORCE 3: THE TRUST FABRIC
YOUR PRIORITY ACTIONS — META-FORCE 3

#3 OF 7 · META-FORCE 4 — DATA, CONTEXT & KNOWLEDGE
Context quality, semantic precision, and knowledge infrastructure determine whether your agents are trustworthy at scale — this is the Tier 2/3 competitive asset that hyperscalers cannot replicate.
Your domain data is your most defensible asset against hyperscalers. Workday has 7,000+ HR workflow records. ServiceNow has 8,500 ITSM deployments of ontological learning. Blue Yonder has supply chain demand signals from thousands of retail-supplier relationships. Veeva has clinical trial and regulatory data from 1,400+ pharmaceutical companies. What is your equivalent? For Tier 2 SaaS, the semantic and contextual data accumulated in customer deployments is the asset that horizontal AI platforms cannot replicate — and it is the asset that makes your agents more reliable in your domain than any general-purpose agent a horizontal can deploy.
T18 ENTERPRISE ONTOLOGY AS STRATEGIC INFRASTRUCTURE
↳ MCP and A2A solve transport. They do not solve meaning. The ontology layer is where the next platform position is being contested.
The semantic gap is the highest-value uncontested territory in the agentic economy. An enterprise with 600+ SaaS applications has as many definitions of ‘customer,’ ‘contract,’ and ‘risk.’ When agents span these systems, semantic conflicts compound — each translation introduces drift, each drift produces error, each error in an autonomous workflow escalates into an incident. Ontological Debt — the accumulated imprecision in how an enterprise defines its core domain objects — compounds at agent execution speed.
WHAT IS CHANGING
- Entity definitions: machine-readable descriptions of core domain objects, valid states, valid transitions, governing rules
- Relationship semantics: how objects relate with cardinality, directionality, and constraint specifications agents can validate
- Business rule encoding: compliance requirements governing actions on domain objects — encoded as ontology, not prompt instructions
- Version control for meaning: semantic definitions version in lockstep with agents; breaking a definition is equivalent to breaking an API
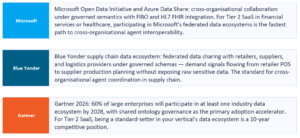
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Agents can act reliably across systems when domain objects have canonical, machine-readable definitions
- Ontological authority creates a structural moat: external agents must validate against your semantic definitions — you become the system of record
- First vertical-specific ontology achieving industry-wide adoption reshapes that industry’s AI ecosystem as HTTP reshaped the web
YOUR ACTIONS
- Commission an ontological audit: document every definition of your top five domain objects across every system — the fragmentation will be the most urgent trust debt you have
- Invest in an enterprise ontology program — not a data governance project — with business leadership, not just data engineers
- Map your schemas to existing standards: FIBO, HL7 FHIR, Schema.org — this is the foundation for ecosystem interoperability
- Open-source your domain schemas where you already lead; build proprietary constraints where you differentiate
T19 THE ENTERPRISE CONTEXT LAYER — CONTEXT AS INFRASTRUCTURE, NOT A PROMPT TECHNIQUE
↳ Governed, fresh, permissioned, provenance-attached context delivered as a runtime service is the infrastructure layer that makes agents trustworthy at scale
Every enterprise AI deployment achieving production reliability has made the same architectural discovery: context is not a prompt engineering problem, it is a platform engineering problem. The Enterprise Context Layer is the unified system managing what information is available to which agents, in what form, with what freshness guarantees, under what permission constraints, and with what provenance metadata attached. Traditional RAG is architecturally insufficient for complex enterprise queries: single-shot retrieval, no iterative reasoning, no permission awareness, no freshness governance.
WHAT IS CHANGING
- Permissioned retrieval engine: entitlements and compliance rules enforced at query level before content reaches context window — outside the model
- Freshness SLA management: freshness tracked by data class; agents refused context that has exceeded its freshness window for the workflow
- Provenance chain: every piece of context carries a tamper-evident record of source, timestamp, permissions, and transformations
- Context quality metrics: coverage, staleness rate, and drift detection as first-class operational KPIs
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Agents act reliably when context is authoritative, fresh, permissioned, and provenance-attached
- Permission violations at context assembly time are eliminated — the most common source of agentic security incidents
- Every agent evidence receipt includes the full context chain-of-custody, enabling auditable and defensible decisions
YOUR ACTIONS
- Architect the Enterprise Context Layer as a first-class platform component with dedicated engineering ownership, SLAs, and monitoring
- Implement permissions-aware retrieval outside the model: entitlements enforced at the retrieval layer, not in the system prompt
- Define freshness SLAs by data class and codify them as runtime constraints, not documentation notes
- Build context chain-of-custody into every agent evidence receipt: what the agent saw, its freshness, its permissions, and what transformations were applied
T20 AGENTIC SEARCH — FROM QUERY-RESPONSE TO SEARCH-AS-REASONING
↳ Traditional RAG is a dead end. Agentic search — plan, retrieve iteratively, evaluate, re-query, synthesize with provenance — is the production architecture for 2026
Enterprise search has been broken for thirty years. Organizations have invested billions in platforms that return links when they need answers. Agentic RAG — where the agent plans what to retrieve, evaluates what it found, determines what additional information is needed, and queries different sources iteratively — is becoming the dominant architecture for production AI systems. OpenSearch’s 2026 roadmap explicitly targets AI agents as the primary user class, with native MCP integration and Agentic Relevance Tuning (ART) as core capabilities.
WHAT IS CHANGING
- Router agent: classifies query type, selects retrieval strategy and source combination
- Iterative retrieval loop: retrieve → evaluate sufficiency → determine gaps → re-query with refined intent → accumulate evidence
- GraphRAG backbone: semantic knowledge graph provides structured reasoning that pure vector search cannot
- Provenance accumulator: every retrieved piece carries source, timestamp, permissions, and confidence score
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Eliminates the hallucination and incomplete-answer failures that are destroying enterprise trust in AI
- Enterprise search becomes the knowledge access layer for every workflow — creating a structural retention moat
- Every workflow that uses the search layer becomes dependent on it; the ISV that owns agentic search owns the dependency
YOUR ACTIONS
- Replace RAG pipelines with Agentic RAG architecture for all production AI workflows
- Build search as a platform capability: governed, multi-source, permission-aware, provenance-tracked retrieval all agents can invoke
- Implement GraphRAG: semantic knowledge graph as backbone for complex multi-hop reasoning queries
- Ship MCP servers for all data sources, document corpora, and knowledge stores
T21 SHARED DATA ECOSYSTEMS AND INDUSTRY ONTOLOGIES
↳ As AI agents span organizational boundaries, common semantics become the interoperability prerequisite — and the standard-setter commands the ecosystem
AI-driven agents increasingly span organizational boundaries — suppliers, regulators, partners. Without common ontologies and governance, inconsistencies in terminology, measurement, and data semantics create friction, risk, and duplicated work. Shared data ecosystems allow firms to collaborate securely while retaining control, traceability, and compliance. The ISV that defines the ontology standard for a vertical becomes as strategically central as the clearinghouses that define financial settlement.
WHAT IS CHANGING
- Sector-specific ontologies: standard definitions for critical entities, relationships, and workflows in regulated industries
- Shared benchmarks and labeling standards: collaborative frameworks for consistent data annotation and validation
- Cross-party governance frameworks: multi-organization agreements defining data access, usage, quality, and audit mechanisms
- Federated access and privacy-preserving analytics: collaborative analysis without exposing raw sensitive data
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Accelerated AI deployment: standardized data enables faster integration into workflows and agentic systems
- Improved accuracy and reliability: reduced semantic misalignment decreases errors in AI predictions and autonomous actions
- Standard-setters create network effects that competitors cannot easily replicate
YOUR ACTIONS
- Participate in industry consortiums to help define and adopt sector-specific ontologies
- Formalize cross-party governance: agreements for access, quality, usage rights, and auditability
- Invest in federated analytics platforms enabling collaboration without sharing raw sensitive data
- Treat shared ecosystem leadership as a strategic asset: long-term influence through standard-setting
T22 DATA LIFECYCLE AND AI INTERACTION GOVERNANCE
↳ AI interaction data — prompts, decisions, execution traces, tool calls — is a governed asset with liability attached, not an operational byproduct
Agentic platforms generate vast interaction exhaust. Without lifecycle controls, enterprises accumulate regulatory exposure, audit gaps, and breach impact from retaining unnecessary sensitive data. GDPR, CCPA, and emerging AI-specific data governance frameworks are formalizing obligations. The market expectation is shifting: store what is needed for accountability, delete what increases liability.
WHAT IS CHANGING
- Tenant-configurable logging: what is stored, at what granularity, and for what retention window — per tenant per workflow
- Right-to-be-forgotten mechanics: automated deletion and anonymization aligned to GDPR and CCPA requirements
- Retention by data class: distinct rules for prompts, execution traces, audit logs, and outputs
- Evidence-by-default without over-retention: action receipts and decision traces stored; raw sensitive content minimized
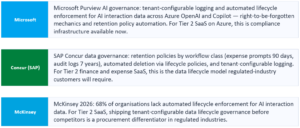
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Reduced liability and breach impact via controlled retention
- Stronger regulatory compliance and audit readiness
- Higher adoption because customers can govern data handling transparently
YOUR ACTIONS
- Define enterprise-wide AI interaction data policies: retain, delete, or anonymize by workflow class
- Automate lifecycle enforcement in runtime and pipelines: policy-as-code for retention is not optional
- Make retention configurable per tenant and per risk tier: SaS requires customer-controllable governance
- Preserve accountability with receipts while minimizing sensitive storage
HOW TO MEASURE YOUR PROGRESS — META-FORCE 4: DATA, CONTEXT & KNOWLEDGE
YOUR PRIORITY ACTIONS — META-FORCE 4

#4 OF 7 · META-FORCE 2 — AGENTIC ARCHITECTURE
The platform battleground shifts from AI features to orchestration maturity, governance primitives, and multi-agent reliability — copilot features are table stakes; mesh architecture is the moat.
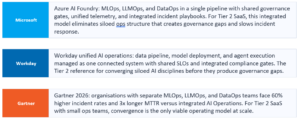
Microsoft has 300,000+ Copilot Studio agents deployed. Salesforce closed 29,000 Agentforce deals. Google Agentspace is in thousands of enterprises. ServiceNow’s Agent Fabric is live across ITSM, HR, and procurement. These platforms are building the orchestration layers that will route enterprise agent traffic. The question for your Tier 2 or Tier 3 platform is not whether to build agentic architecture — it is whether your capabilities will appear in that routing layer as first-class execution surfaces or as legacy features that orchestration layers work around.

T06 FROM COPILOT FEATURES TO AGENT MESH ARCHITECTURE
↳ The competitive battleground shifts from AI features to orchestration maturity, governance primitives, and multi-agent reliability
Gartner predicts 40% of enterprise applications will be integrated with task-specific AI agents by end of 2026. By 2027, one-third of agentic implementations will combine agents with different skills for complex tasks. By 2028, agent ecosystems will enable networks of specialized agents to dynamically collaborate across applications and business functions without users interacting with individual apps. The platform that cannot orchestrate across systems with governance and traceability built in will be invisible to orchestration layers regardless of model quality.
WHAT IS CHANGING
- Planner-Executor separation: planning is reviewable; execution constrained to approved action surfaces
- Supervisor-Specialist swarms: narrow specialists coordinated by a supervisor rather than one generalist
- Governance primitives native: approvals, delegation, tool constraints, and kill-switches embedded in architecture
- Standards interoperability: MCP for agent-to-tool, A2A for agent-to-agent — not optional, not future consideration
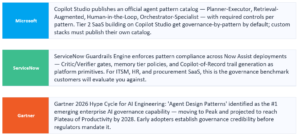
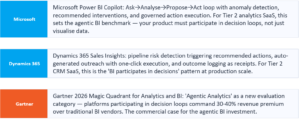
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Higher reliability at scale: fewer multi-system workflow failures and inconsistent outcomes
- Faster deployment of autonomous workflows: enterprises reuse orchestration patterns instead of reinventing coordination
- Stronger defensibility: platforms providing robust orchestration and governance become the default automation substrate
YOUR ACTIONS
- Build an agent orchestration layer as a core platform control plane with policies, audit, delegation, and versioning
- Make every major capability agent-callable via MCP with stable, governed contracts and explicit constraints
- Publish an enterprise agent pattern catalog: approved patterns, required controls, and prohibited patterns
- Treat traceability as a product requirement: every action produces intent, context, policy, tool calls, and side effects
T07 AGENT SURFACES BECOME THE NEW FRONT DOOR
↳ Users express intent in their primary work context and expect execution — platforms without agent surfaces become invisible
Users will not context-switch across a dozen applications to complete a workflow. They will express intent in Teams, Slack, CRM, service desks, or line-of-business systems and expect execution. Platforms that lack agent-ready surfaces risk becoming invisible even if their underlying capabilities are strong — because orchestration layers route around products that lack MCP surfaces.
WHAT IS CHANGING
- Surface integration: agents embedded in collaboration and operational systems, not bolted onto a product UI
- Work-graph alignment: agents operate with workflow context, tasks, approvals, and state
- Admin-led deployment: secure scaling depends on IT-controlled rollout, policy, and permissions
- Uniform action APIs: headless, consistent capability surfaces invokable by UI, chat, API, or external agent
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Higher adoption: agents meet users where they already work; training and navigation costs fall
- Faster scale with control: admin-led deployment reduces shadow AI and inconsistent behavior
- Greater stickiness: work-graph integration increases dependency and retention
YOUR ACTIONS
- Make agent surfaces the primary product strategy: design for intent-in, outcome-out
- Integrate with the work graph: tasks, approvals, and process state as first-class inputs to agent execution
- Enable secure admin-led scaling: governance controls and deployment workflows ship with the product
- Standardize the action layer: one governed execution surface invoked by all interfaces and external agents
T08 INTENT BECOMES THE CONTROL PLANE — INTENT → ROUTING → EXECUTION → EVIDENCE
↳ Predictable, auditable, risk-aware execution at scale requires a consistent control loop — not raw prompts
As agent fleets span workflows and organizational boundaries, raw prompts and static flows break down. Enterprises need systems that interpret intent, classify risk, and enforce execution rules so automation scales without increasing incidents. Intent alignment is also a trust requirement: buyers want to know what the agent is doing, why, under which policy, and what the rollback path is.
WHAT IS CHANGING
- Intent routing: explicit routing logic selects the right workflow, model/tool, and approval path based on risk and context
- Execution posture control: suggest → draft → execute → escalate, governed by thresholds and policy — not model behavior
- UX affordances for intent: users can see and adjust what the system intends to do before side effects occur
- Evidence-by-default: every intent-triggered action produces traceable receipts and audit trails
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Higher productivity: fewer handoffs, more accurate and proactive completion
- Reduced risk: escalation and audit prevent unintended consequences
- CFO-ready economics: intent-to-outcome telemetry improves cost-per-resolution and outcome pricing confidence
YOUR ACTIONS
- Standardize an intent-first architecture across all workflows: Intent → Routing → Execution → Evidence
- Define autonomy rules explicitly: when agents execute, when they draft, when they must escalate
- Mandate evidence trails for all consequential actions: receipts plus reversibility paths
- Measure intent-to-outcome efficiency: completion rate, reversals, escalations, time-to-value
T09 MULTI-MODEL INTELLIGENCE ARCHITECTURE — BEST OUTCOME ECONOMICS, NOT BEST MODEL
↳ Single-model strategies create cost volatility, latency bottlenecks, and governance risk — the goal is outcome economics with controlled risk
A single large model for all workflows creates unpredictable COGS, governance risk, and latency bottlenecks. Enterprises want sensitive workloads handled locally with constrained models; routine tasks done cheaply; high-stakes work routed through higher-assurance stacks. Multi-model routing becomes a SaS requirement because it stabilizes COGS and improves reliability under outcome-based pricing.
WHAT IS CHANGING
- Hybrid intelligence: SLMs for routine work, frontier models for complex reasoning, specialized engines for regulated domains
- Strategic routing: dynamic assignment by cost, latency, risk tier, and data sensitivity
- Redundancy and fallback: failover paths between engines for mission-critical workflows
- Track outcomes by model: accuracy, completion rate, reversal rate, cost-per-task — to optimize routing over time
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Lower cost-to-serve: fewer unnecessary frontier calls; improved margin stability
- Higher reliability: reduced dependency on one model/provider; better resilience
- Better compliance posture: model selection aligned to sovereignty and regulatory constraints
YOUR ACTIONS
- Make multi-model architecture the platform default: SLMs, frontier, retrieval, and specialized engines
- Implement routing logic as a platform primitive: cost, latency, risk, sensitivity — not a manual config
- Engineer failover for critical workflows: redundancy is a trust feature, not a luxury
- Align model choices to SaS economics: stable COGS is the condition for sustainable outcome pricing
T10 AGENT DESIGN PATTERNS BECOME THE GOVERNANCE LANGUAGE
↳ Pattern governance is the only model that scales — it is easier to approve a known pattern with defined controls than to review one-off agent behavior
As agent fleets grow, teams invent inconsistent approaches to planning, memory, tool use, and oversight — creating an agent zoo that governance cannot control. Patterns become the unit of architecture and the unit of governance. Risk reviews become tractable when they are pattern-based rather than bespoke.
WHAT IS CHANGING
- Critic/Verifier gates: second-pass checks for policy, grounding, tool safety, and schema validity before execution
- Human-in-the-loop vs human-on-the-loop: engineered oversight with thresholds, sampling, alerts, stop-the-line triggers
- Memory tiers with policy: task, episodic, semantic — retention and decay enforced, not prompted
- Copilot-of-record trails: decision logs, evidence, and rollback capability for high-stakes work
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Faster shipping with fewer incidents through reuse of proven patterns
- Lower governance friction because risk reviews become pattern-based
- Higher trust due to evidence-backed execution and clear rollback paths
YOUR ACTIONS
- Publish an enterprise agent pattern catalog with approved patterns, required controls, and prohibited patterns
- Standardize governance-by-pattern: pattern selection explicit in design reviews and tied to autonomy tiers
- Mandate receipts and rollback for all consequential workflows: copilot-of-record as standard
- Define memory policy as enterprise policy: what can be stored, retention windows, entitlements, deletion
T11 AGENT RUNTIME AS CORE PRODUCT INFRASTRUCTURE
↳ The control plane for versioning, rollout, permissions, auditability, and safe execution is the mechanism that makes SaS credible at scale
You cannot scale autonomous systems with ad hoc deployments. Enterprises need consistent behavior, traceability, and governance under incident pressure. The agent runtime becomes the mechanism that makes SaS credible: it enforces policy, controls tool access, supports staged rollout and rollback, and generates evidence-by-default. Runtime maturity is now a procurement differentiator.
WHAT IS CHANGING
- Versioning and rollout management: progressive delivery, canarying, and instant rollback for agents and workflows
- Permission and tool registries: least-privilege access and approved tool catalogs enforced at runtime
- Audit trails by default: every action yields traceable evidence for compliance and liability
- Governance enforced at runtime: policies, escalation paths, and approvals are executed, not documented
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
- Higher adoption: stakeholders trust systems that can prove controlled execution
- Lower operational risk: fewer rogue behaviors and faster containment during incidents
- SaS defensibility: runtime maturity is a procurement differentiator and retention moat
YOUR ACTIONS
- Treat runtime as product infrastructure: invest in rollout, rollback, permissions, and observability
- Make evidence non-optional: receipts for every consequential action
- Enforce governance in code: approvals, delegation, and policy gates at runtime — not in documentation
- Link runtime telemetry to the Revenue Intelligence Layer: connect agent versions to business outcomes
HOW TO MEASURE YOUR PROGRESS — META-FORCE 2: AGENTIC ARCHITECTURE
YOUR PRIORITY ACTIONS — META-FORCE 2
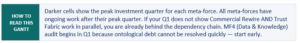
#5 OF 7 · META-FORCE 6 — OPERATIONAL TRANSFORMATION
Agentic delivery requires agentic operations — the six trends here separate Tier 2 SaaS platforms that scale SaS from those that remain in perpetual pilot mode.
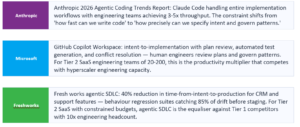
The 95% pilot failure rate is an operational problem masquerading as a capability problem. Behaviour drift, governance gaps, siloed ops disciplines, and the absence of a Revenue Intelligence Layer connecting engineering decisions to commercial outcomes — these are the operational failures that kill agentic deployments at scale. For Tier 2 SaaS competing against Tier 1 platforms with 10x engineering headcount, the operational transformation in this meta-force is the equaliser. A Tier 2 platform with mature AgentOps, agentic SDLC, and GCC 3.0 delivery can outship and outdeliver a Tier 1 platform with traditional delivery infrastructure.
The agentic SDLC is the Tier 2 SaaS equaliser. When behaviour regression suites catch drift before it reaches production, and when the Revenue Intelligence Layer connects every release to its NRR impact — a 50-person engineering team competes with a 500-person team on delivery quality. The organisations that build this operational infrastructure will outship their category for the next decade.
— Gaurav Agarwaal, SVP – Global Head Solution Engineering & Field CDAIO, Onix
T27 AGENTIC SDLC — THE SOFTWARE FACTORY THAT SHIPS ITSELF
↳ The delivery constraint shifts from engineering capacity to intent clarity, governance maturity, and evaluation rigor
Anthropic’s 2026 Agentic Coding Trends Report documents that engineering teams have discovered AI can now handle entire implementation workflows: writing tests, debugging failures, generating documentation, navigating complex codebases. The deeper shift: when agents handle implementation, the new reliability risk is behavioral drift — a system that changes behavior without any code change because a model updates, a routing rule shifts, or a context source refreshes. This cannot be detected by traditional testing and requires continuous behavioral monitoring with automated rollback triggers.
WHAT IS CHANGING
- Behavior regression suites: automated evaluation across the full intent specification space — not just happy paths
- Pattern governance: approve agent patterns (orchestration architectures, memory models, tool access) rather than reviewing individual code changes
- Adversarial QE: attacker agents probe prompt injection, tool misuse, policy bypass, and cross-agent failure modes as release gates
- Revenue Intelligence Layer connection: every release tagged with full configuration; post-release business outcomes attributed to specific engineering decisions
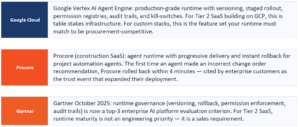
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster intent-to-production with fewer incidents: agents handle implementation, humans govern patterns
• Behavioral drift becomes detectable and reversible rather than a silent production failure
• Engineering decisions governed by outcome data: completion rate, reversal rate, cost-per-outcome linked to specific releases
YOUR ACTIONS
1. Build behavior regression suites before deploying agents to production — if you lack an evaluation suite, you are deploying blind
2. Treat prompts, model versions, routing configurations, and tool access as versioned artifacts with staged rollout and automated rollback
3. Implement continuous behavioral monitoring with anomaly detection and policy-bounded automated rollback
4. Connect SDLC to the Revenue Intelligence Layer: tag every release with its full configuration and instrument post-release business outcomes
T28 AGENTOPS DISCIPLINE AND BEHAVIORAL OBSERVABILITY
↳ Observability moves beyond uptime to track agent behaviors, decision flows, and workflow outcomes — behavioral traceability is both an operational backbone and a customer-facing trust feature
With agentic systems executing multi-step workflows, traditional logs and uptime dashboards do not explain why an agent acted, what context it used, what tools it invoked, or what the outcome and cost were. Without behavioral traceability, MTTR rises, governance weakens, and trust breaks — especially under outcome-based commercial models where you are accountable for completion quality.
WHAT IS CHANGING
• Behavioral traceability chain: intent → model/tool → data → agent action → outcome → cost
• Behavioral SLOs: task success rate, escalation frequency, safe-failure rate, cost per completed action
• Embedded AIOps: detect drift, inefficiency, and anomalies and remediate autonomously within policy limits
• Control tower: centralized visibility into agent workloads, drift, escalations, and operational anomalies
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster issue resolution: traceability reduces MTTR and simplifies root cause analysis
• Improved reliability: early anomaly detection prevents workflow failures before they surface as incidents
• Better SaS economics: cost-per-outcome becomes observable, attributable, and optimizable
YOUR ACTIONS
1. Institutionalize AgentOps as a core function with ownership, behavioral SLOs, and incident playbooks
2. Expand observability beyond uptime: include intent, actions, tool use, outcomes, and cost in every trace
3. Make telemetry customer-facing where it increases trust: completion rate, reversals, escalations
4. Feed AgentOps telemetry into the Revenue Intelligence Layer: outcomes and cost-per-completion tied to versions
T29 INTEGRATED OPS — ONE DISCIPLINE FOR MODELOPS, LLMOPS, MLOPS, AND DATAOPS
↳ Siloed operations across data, models, and workflows create the exact failure modes that block SaS scale
In agentic platforms, the unit you operate is not a model — it is behavior across intent, context, tool calls, and side effects. Integrated Ops is how you keep that behavior stable under constant change. Siloed teams managing data, models, prompts, and agents independently will produce drift, governance gaps, brittle rollouts, and costly incidents.
WHAT IS CHANGING
• Unified lifecycle management: data, models, prompts, tools, and agents managed as one connected system
• Continuous evaluation: monitor drift, bias, underperformance, and policy violations continuously — not quarterly
• Resilience engineering by default: staged rollout, rollback, redundancy, and safe-failure playbooks
• Policy-driven automation: governance enforced through code and runtime gates, not manual reviews
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster, safer releases: fewer failed deployments and fewer pilot-to-production collapses
• Lower operating cost: reduced duplication across ops teams and fewer expensive incidents
• Audit readiness: traceable evidence across the lifecycle becomes standard procurement collateral
YOUR ACTIONS
1. Converge Ops disciplines into one operating model with shared SLOs and incident playbooks
2. Instrument end-to-end traces: intent → context → tool calls → outcomes → rollbacks
3. Build drift gates for prompts, tools, workflows, and policies — not just models
4. Make compliance enforceable via policy-as-code at runtime
T30 GCC 3.0 — FROM CAPACITY CENTER TO AGENTIC SOFTWARE FACTORY
↳ The shift is from providing capacity to owning end-to-end outcomes powered by AI agents, telemetry-led operations, and continuous delivery
Traditional GCCs optimized for labor arbitrage and execution efficiency. The new expectation is cloud-speed delivery with governance: agents generate, verify, and deploy changes; monitoring operates continuously; and outcomes are measured against business KPIs, not headcount efficiency. This directly supports SaS: operated outcomes require operated engineering.
WHAT IS CHANGING
• Factory lanes by domain: Product, Platform, Runtime, Data, Trust, and Reliability/FinOps — each lane owns measurable outcomes
• Cross-functional pods: end-to-end ownership from intent/specification to production reliability
• Telemetry-led delivery: progress, risk, cost, and release health tracked continuously — not via status rituals
• 24×7 continuous improvement: monitoring, automation, and remediation as factory capability
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster release throughput without proportional headcount growth
• Improved reliability and lower MTTR via continuous monitoring and automated remediation
• Better business alignment: GCC output measured against business KPIs, not activity metrics
YOUR ACTIONS
1. Redesign GCCs around outcomes — completion, reliability, cost-per-outcome — not capacity metrics
2. Implement cross-functional agentic pods with clear accountability from spec to production
3. Make telemetry the delivery backbone: tie engineering work to outcome metrics via the Revenue Intelligence Layer
4. Embed FinOps and reliability engineering as core GCC disciplines — not separate functions
T31 FORWARD DEPLOYED ENGINEERS AND DOMAIN PODS
↳ In agentic SaS, the hard work is making autonomy reliable in messy operational reality: semantics, context quality, evaluation benchmarks, escalation rules, and cost-per-completion
Traditional FDE roles focused on deployment and integration. In agentic SaS, FDEs must own the semantics, reliability, and measurable impact of AI solutions — ensuring autonomous agents operate effectively in complex, multi-tenant enterprise environments. They are the bridge between business context and agentic delivery, and the mechanism that transforms pilots into production.
WHAT IS CHANGING
• Elite domain-embedded engineers: deep workflow and compliance understanding, not generic integration expertise
• Ownership of domain assets: datasets, evaluation suites, context KPIs, and outcome baselines — not just deployment
• Cross-functional domain pods: engineering, reliability, AI ops, and product experts delivering end-to-end outcomes
• Measured by outcomes: reliability, cost-per-completion, throughput — not lines of code or days on-site
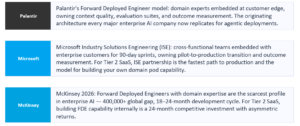
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster pilot-to-scale: domain fit and governance are engineered early rather than discovered in production
• Higher trust in autonomy: domain-grade evaluations and escalation design built from first-principles understanding
• Better unit economics: real-world routing and evaluation reduce rework and runaway cost
YOUR ACTIONS
1. Build FDE/domain pods as a productized delivery capability — this is your FDIE integration and enablement wrapper operationalized
2. Standardize domain evaluation: acceptance thresholds, failure modes, and escalation paths per workflow
3. Tie pods to the Revenue Intelligence Layer: outcomes and cost-per-completion mapped back to releases and agent versions
4. Scale the pattern: replicate domain pods by vertical and workflow — not by generic implementation teams
T32 TELEMETRY-LED DELIVERY AND PRODUCT INTELLIGENCE AS REVENUE ARCHITECTURE
↳ Product analytics stops being insight for dashboards and becomes the commercial backbone: proving value continuously, triggering the right commercial action, protecting NRR
In SaS, value is not ‘users active’ but work completed. If you cannot prove outcome attainment continuously, you cannot defend outcome pricing, expansion, or renewals. Telemetry becomes the commercial backbone: it turns completion quality into measurable value proof and makes monetization less dependent on sales narratives. PLG and RevOps converge inside the product — value proof cards, expansion prompts, renewal readiness, and risk flags appearing where users act.
WHAT IS CHANGING
• Telemetry as a governed asset: journey completion, time-to-value, struggle events, and outcome attainment as renewal and expansion signals
• PLG + RevOps convergence inside the product: expansion prompts and renewal readiness surfaced in-product
• AI makes telemetry executable: signals converted into actions — risk detected → outreach created → offer generated → impact tracked
• Revenue Intelligence Layer: releases and agent versions linked to completion rate, reversal rate, NRR, and margin
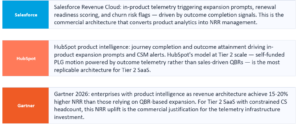
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Higher NRR: proactive save and expansion driven by real value signals rather than QBR narratives
• Better margin discipline: outcome telemetry supports outcome pricing and manages variable AI COGS
• Faster GTM loops: what works becomes visible quickly; what fails gets corrected before quarter-end
YOUR ACTIONS
1. Define value proof per segment: which outcomes matter, how they are measured, and how they are shown in-product
2. Instrument top journeys deeply: completion, time-to-complete, reversals, escalations, and friction points
3. Build in-product action cards: every insight carries next best action, owner, and expected impact
4. Govern telemetry like a product contract: standard event definitions, quality checks, audit-ready linkage to commercial actions
HOW TO MEASURE YOUR PROGRESS — META-FORCE 6: OPERATIONAL TRANSFORMATION
YOUR PRIORITY ACTIONS — META-FORCE 6
#6 OF 7 · META-FORCE 5 — THE EXPERIENCE LAYER
Differentiation shifts from feature depth to completion quality — the experience layer is where your customers see and judge your agentic investment.
Your users will soon stop interacting with your application directly. They will express intent in Teams, Slack, or voice — and expect completion. The question is whether that completion happens inside your platform or whether an orchestration layer routes around your UI to get it done through a competitor’s agent surface. For Tier 2 SaaS, the experience architecture decision is also a distribution decision: agent surfaces embedded in the work graph reach users without marketing spend; traditional UI requires users to navigate to you.
The best product feature is the one your users never notice because it made their work faster. Tier 2 SaaS companies that measure completion quality — task success rate, reversal rate, time-to-value — rather than engagement time and feature breadth will win the next generation of enterprise renewals. Your buyers’ employees are being measured on outcomes. Your product should be too.
— Gaurav Agarwaal, SVP – Global Head Solution Engineering & Field CDAIO, Onix
T23 INTELLIGENT UX FOR AI-NATIVE APPS — FROM INTERFACE TO AMBIENT INTELLIGENCE
↳ The chat box is dead. AI-native UX is not AI features in an app — it is an app where intelligence is structural, invisible, and completion-centric
By 2026, the design paradigm has inverted. The best AI-native applications treat AI as an invisible ambient layer — not a feature to interact with, but the structural mechanism by which the entire application becomes responsive to intent. Google’s A2UI protocol (February 2026) enables agents to generate structured UI layouts that are securely passed as messages, not executable code, rendered by the client’s own design system. Visual confidence indicators, streaming-first rendering, and intent-state-aware navigation are the production patterns defining the category.
WHAT IS CHANGING
• Generative UI: interfaces generated in real time based on user context and intent — not static menus for every user
• A2UI: agent-generated interfaces as structured messages, client-rendered with own design system — the production mechanism for agentic UX
• Visual confidence indicators: selective UI signals communicating AI certainty on high-stakes outputs — not on every response
• Ambient intelligence: the application adapts, anticipates, and reduces cognitive load without announcing itself as AI
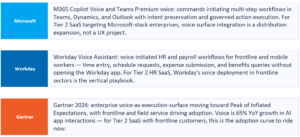
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Higher adoption: users trust systems that feel responsive to intent rather than requiring explicit AI interaction
• Differentiation moat shifts to completion quality — platforms leading with UI breadth over execution depth lose
• Completion quality as the primary UX metric: success rate, reversals, escalations, time-to-value replace engagement
YOUR ACTIONS
1. Retire the AI pane: redesign workflows so intelligence is structural, not additive as a sidebar or chat overlay
2. Implement A2UI for agent-generated interfaces: agents surface rich branded interactive results as cards, not text responses
3. Instrument visual confidence indicators for high-stakes outputs selectively — over-indication destroys trust in all outputs equally
4. Redesign the completion surface: done means evidenced, reversible, and with a clear next action
T24 AGENTIC BI REPLACES DASHBOARDS WITH DECISION LOOPS
↳ Enterprises shift from ‘look at metrics’ to Ask → Analyze → Propose → Simulate → Act
Static dashboards cannot keep pace with the speed and complexity of modern operations. Agentic BI participates in decision loops instead of passively reporting. All recommendations and actions are auditable, supporting compliance and accountability. The integration pattern: BI agents pull live data, surface options and risks, simulate alternatives, and execute governed actions — all within the operational workflow, not in a separate portal.
WHAT IS CHANGING
• Decision loops instead of dashboards: Ask → Analyze → Propose → Simulate → Act
• Embedded decisioning: agents surface options, risks, and next steps inside the workflow
• Simulation-first execution: test what-if scenarios before committing actions — reduces costly mistakes
• Traceability: reasoning, simulations, and actions logged as receipts supporting trust and compliance
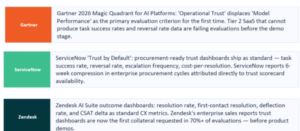
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster evidence-backed decisions with fewer errors
• Reduced lag from insight to outcome: analysis becomes directly executable
• Better governance and action alignment through auditable decision chains
YOUR ACTIONS
1. Shift from reporting to decision loops: require BI to recommend and — where safe — execute actions
2. Mandate auditability: every recommendation and action must produce an evidence trail
3. Integrate BI agents directly into operational workflows — where the work happens
4. Measure success by decision accuracy, speed, and risk reduction — not dashboard engagement
T25 VOICE-FIRST WORKFLOWS AND MULTIMODAL EXPERIENCES
↳ Voice becomes a first-class execution surface — not an accessibility feature, not a search interface, but a mechanism for completing governed work
Voice usage in AI applications has grown 65% year-on-year. Enterprises need lower cognitive load, faster execution, and support for frontline and remote workers who cannot rely on keyboards or screens. Voice and multimodal engines are now context-aware and integrated with operational systems — turning interaction into completion. The design shift: voice must be a first-class input path in the primary action bar, not a buried microphone icon.
WHAT IS CHANGING
• Voice as execution layer: interpret intent, maintain context across interactions, initiate multi-step workflows
• Multimodal continuity: voice input producing text, visual, or notification outputs as appropriate to context
• Emotion and context awareness: urgency and tone cues inform escalation and confirmation paths
• System integration: voice agents update records, trigger workflows, notify teams across CRM, collaboration, and PM tools
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Faster task completion: less navigation overhead; higher workflow throughput
• Higher adoption: natural interfaces expand usage beyond desk workflows — critical for frontline workers
• Lower error and friction: hands-free execution reduces interruptions and rework
YOUR ACTIONS
1. Treat voice as an execution surface with the same design investment as visual UI
2. Design multimodal receipts: every voice-initiated action yields confirmation, evidence, and reversibility cues
3. Measure voice outcomes: completion speed, error reduction, adoption by user segment
4. Build global readiness: multilingual and accent-robust capability as baseline, not enhancement
T26 HYPER-PERSONALIZATION WITH GOVERNANCE — RESPONSIBLE PERSONALIZATION AT SCALE
↳ The win condition is personalization you can explain, control, and prove — not personalization you can merely generate
AI personalization can boost engagement and satisfaction — but unmanaged personalization creates privacy backlash, trust erosion, and regulatory risk. Adobe’s 2026 AI and Digital Trends report finds only 44% of organizations have implemented a measurement framework for generative AI personalization, and 31% for agentic AI personalization. In enterprise platforms, governed personalization is the commercial durable form — because personalization you cannot audit is a liability.
WHAT IS CHANGING
• Dynamic context-aware personalization: interfaces and recommendations adapting in real time to behavior and situational signals
• Transparent consent controls: explicit opt-in, clear explanations of how and why data is used, user control
• Ethical data governance: purpose limitation, data minimization, and auditability as built-in constraints — not retrofit
• Privacy-first stacks: consent management and first-party data practices aligned to GDPR and CCPA
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Higher conversion and retention where personalization is trusted and controllable
• Lower compliance risk via consent-bound, auditable personalization
• Stronger SaS posture: personalization becomes a governed outcome accelerator, not a liability
YOUR ACTIONS
1. Build consent as a product primitive: opt-in controls and transparency by default — aligned with GDPR and CCPA
2. Enforce ethical constraints in code: purpose limitation, minimization, and audit trails as runtime gates
3. Tie personalization to measurable outcomes — completion, time-to-value — not engagement proxies
4. Instrument trust signals: opt-out rate, override frequency, complaint rate, and policy violations
HOW TO MEASURE YOUR PROGRESS — META-FORCE 5: THE EXPERIENCE LAYER
YOUR PRIORITY ACTIONS — META-FORCE 5
#7 OF 7 · META-FORCE 7 — ECOSYSTEM & HUMAN TRANSFORMATION
The ecosystem positions being established in 2026 will be the competitive facts of 2028 — B2B2A, vertical consolidation, and machine customers define where Tier 2/3 SaaS fits.
The ecosystem positions being established in 2026 will be the competitive facts of 2028. ServiceNow is claiming ITSM semantic authority. Veeva is claiming life sciences. Blue Yonder is claiming supply chain. Workday is claiming HCM. In every vertical, a window is currently open to establish domain-truth authority that makes you indispensable to the entire ecosystem. For Tier 2 SaaS, this is not an abstract strategic discussion — it is a decision about whether you will be the ontological authority in your vertical or the vendor that must be compatible with someone else’s definitions.
Every vertical has a semantic authority position available right now — and very few Tier 2 SaaS companies are competing for it. Publish your domain ontology. Define your canonical object schemas. Make your regulatory mappings machine-readable. The company that establishes semantic authority in a vertical before 2027 will earn routing preference from every orchestration layer in that vertical for the decade that follows.
— Gaurav Agarwaal, SVP – Global Head Solution Engineering & Field CDAIO, Onix
T33 AGENTIC COMMERCE AND THE M2M ECONOMY
↳ Marketplaces evolve from connectors and listings to agent-to-agent commerce — the shift from human-mediated procurement to machine-mediated trusted execution
As agents become capable of end-to-end execution, the bottleneck moves from integration to trust. Enterprises demand marketplaces that certify actions, enforce policy, and produce audit-ready evidence. In this model, the valuable SKU is not your API — it is a verified action set that agents can safely invoke. McKinsey projects agentic commerce to reach $3-5 trillion globally by 2030.
WHAT IS CHANGING
• Certified actions as currency: workflows carrying verification signals for compliance, performance, and auditability
• ACP and UCP for agent commerce: IBM’s Agent Commerce Protocol and Google’s Universal Commerce Protocol handle payment, fulfillment, and transaction semantics
• Autonomous transactions: procurement, negotiation, and settlement increasingly agent-driven — compressed cycle times
• Trust-first participation: SLAs, audit trails, and safe-failure handling are mandatory, not differentiators
WHO IS ALREADY DOING IT

WHAT IT MEANS FOR YOUR BUSINESS
• Faster cycle times: machine-mediated purchasing and execution compress procurement latency
• New monetization: certified action sets become premium offerings — earn revenue even when another agent takes the action
• Lower risk: built-in evidence and compliance reduce liability and adoption friction
YOUR ACTIONS
1. Design products for agentic execution: every workflow callable, constrained, and observable
2. Publish certified action sets with reliability targets, compliance posture, and audit artifacts
3. Build for agent-to-agent commerce: automated contracting, billing, and verification-ready logs
4. Make trust throughput a KPI: adoption, repeat invocation, reversals, escalation rates, safe-failure frequency
T34 ECOSYSTEM MESH, B2B2A, AND AGENT NETWORK EFFECTS
↳ B2B2A — business-to-business-to-agent — is the new buyer layer; orchestration owners control demand flow and compound network effects
When agents can switch tools instantly, distribution advantage shifts from best UI to default skill in the orchestration layer. Ecosystem winners compound faster because every successful agent-completed workflow improves routing, trust signals, and future completion rates — creating agent-to-agent network effects that are structurally different from traditional SaaS network effects. Orchestration ownership becomes competitive gravity.
WHAT IS CHANGING
• Orchestration ownership as competitive gravity: whoever controls routing controls demand flow
• Network effects become agent-to-agent: more callable skills + better context + more verified outcomes → compounding advantage
• MCP-ready capability publishing: standardized, constrained surfaces reduce integration friction and increase reuse
• Trust gates ecosystem participation: identity, permission manifests, provenance — validated outside the model
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Winner-take-most dynamics: orchestration owners can bundle, steer demand, and shape economics
• Faster partner scaling: standardized callable surfaces accelerate ecosystem growth
• Governance becomes monetizable: safer ecosystems attract enterprise-grade adoption at premium
YOUR ACTIONS
1. Decide your ecosystem role explicitly: orchestrator, capability provider, or both — strategy differs radically
2. Publish stable skills and intents with constraints, auditability, and predictable semantics — machine-callable, not UI-dependent
3. Enforce agent trust controls outside the model: permission manifests, validations, safe tool access
4. Protect differentiation with domain truth and verified outcome reliability — the assets ecosystems pay premium for
T35 VERTICAL SAAS CONSOLIDATION AND DOMAIN-TRUTH POSITIONING
↳ UI-led vertical SaaS faces a hard fork: become a trusted machine-accessible domain-truth layer or be absorbed by horizontal orchestration platforms
Horizontals that own orchestration can route intent across tools, making point products interchangeable unless they control defensible assets: proprietary domain datasets, regulatory mappings, benchmarks, and verified workflow reliability. In B2B2A markets, being best in UI matters less than being trusted enough for agents to act on. Bain’s analysis is direct: miss the semantic layer and your platform becomes a silent back end while semantic gatekeepers harvest the margin.
WHAT IS CHANGING
• Domain truth as the moat: definitions, rules, constraints, and compliance semantics more valuable than feature breadth
• Machine-usable domain layer: publish machine-consumable semantics, policies, and callable skills
• Contracted quality: accuracy, freshness, and compliance coverage as SLO-driven commercial commitments
• Consolidation accelerates when horizontals own orchestration: UI-led vendors face the highest disruption risk
WHO IS ALREADY DOING IT
WHAT IT MEANS FOR YOUR BUSINESS
• Pricing power for domain-truth leaders: verified semantics and outcomes justify premium models
• Faster enterprise adoption: trusted vertical truth reduces ambiguity and governance friction
• New partnership leverage: vertical truth providers become preferred components inside broader ecosystems
YOUR ACTIONS
1. Define your truth assets: proprietary datasets, regulatory mappings, benchmarks, validated workflows — invest where you can own defensibility
2. Publish callable domain capabilities: expose trusted intents and constraints for agent consumption — avoid UI-only defensibility
3. Guarantee quality with SLOs: accuracy, freshness, and compliance coverage become contractual differentiators
4. Decide now: consolidator, specialist truth layer, or acquisition target — then build accordingly
T36 AGENTIC CUSTOMER EXPERIENCE AND THE MACHINE CUSTOMER
↳ By 2029, 80% of routine CX resolved autonomously — but the bigger disruption is the inverse: your customers will use agents to negotiate, escalate, and purchase on their behalf
Gartner predicts agentic AI will autonomously resolve 80% of common customer service issues by 2029, with a 30% reduction in operational costs. Cisco projects 56% of customer support interactions will use agentic AI by mid-2026. But the structurally more consequential shift is the B2B2A inversion: half of all customer service requests will soon originate from agents acting on behalf of human users. Your customers will deploy their own agents to handle routine interactions with your platform. Service design must serve machines, not just humans.
WHAT IS CHANGING
• Tier 0 autonomous resolution: well-defined, high-volume, low-exception workflows — fully autonomous by end of 2026
• Machine-legible service APIs: structured response schemas and deterministic outcome specifications for customer agents to consume and verify
• Four CX layers: Tier 0 Autonomous, Supervised Autonomous, Human-on-the-loop, Machine-to-Machine Service
• Agent-to-agent dispute resolution protocols: when your service agent and their customer agent disagree, who arbitrates?
WHO IS ALREADY DOING IT
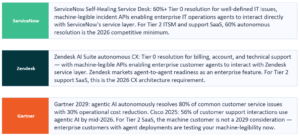
WHAT IT MEANS FOR YOUR BUSINESS
• 78% of organizations expect agentic AI to handle at least half of customer support within 18 months — Adobe 2026
• 30% reduction in operational costs at 80% autonomous resolution — Gartner 2029 projection
• Brands that fail to design for machine customers will face CX degradation as agent-to-agent interactions replace human-to-agent interactions
YOUR ACTIONS
1. Achieve Tier 0 autonomous resolution for your top ten high-volume support workflows by end of 2026
2. Design your service layer for machine customers: machine-legible APIs, structured response schemas, deterministic outcome specifications
3. Build a measurement framework before you deploy: what does successful autonomous resolution look like — and what is the reversal rate target?
4. Define the agent-to-agent dispute resolution protocol now — before it becomes a regulatory or commercial liability
HOW TO MEASURE YOUR PROGRESS — META-FORCE 7: ECOSYSTEM & HUMAN TRANSFORMATION
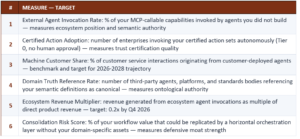
YOUR PRIORITY ACTIONS — META-FORCE 7
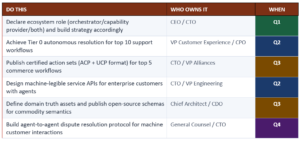
7 MISTAKES THAT WILL COST TIER 2/3 SaaS THIS CYCLE
Each pattern is visible in real Tier 2 and Tier 3 SaaS deployments right now. Each one looks like a reasonable decision at the time. Ask honestly: which of these is us?
MISTAKE 1 AGENT WASHING
Why you might be doing it: Fast demos, positive press, reassures boards that the company is ‘doing AI.’
Why it will cost you: Industry analysts estimate fewer than 130 of thousands of claimed AI agent vendors are building genuinely agentic systems. Procurement teams are developing technical criteria to distinguish genuine agentic capability from washing. The tell: if your agent cannot handle unexpected state, escalate gracefully, or produce a traceable evidence trail, it is a bot with a marketing rename. The cost compounds when enterprise buyers discover the gap at scale.
MISTAKE 2 THE MODEL IS THE CONTROL PLANE
Why you might be doing it: Fewer constraints, faster to ship, the model can decide — reduces upfront governance investment.
Why it will cost you: Prompt injection becomes an execution risk, not a content risk. Tool misuse and policy bypass are inevitable at scale. McKinsey identifies uncontrolled autonomy and lack of traceability as the top two risks in agentic AI deployments — both are direct consequences of using the model as the control plane. Deterministic controls must exist outside the model: policy engines, action validators, runtime gates.
MISTAKE 3 THE DATA TOLL BLINDSPOT
Why you might be doing it: Modeling AI ROI based on compute and model costs only — the visible cost line items.
Why it will cost you: API connection fees and data access tolls are becoming the new cloud egress charges. Constellation Research identifies data tolls as potentially the biggest risk to scaling AI agents — larger than compute costs. ISVs that do not instrument and budget for data access costs at the workflow level will find their outcome pricing models insolvent at scale.
MISTAKE 4 COPILOT ON BROKEN PROCESSES
Why you might be doing it: Fast demo cycles, visible AI adoption, minimal process change — appears low-risk.
Why it will cost you: Agents amplify process flaws. Unclear ownership, inconsistent definitions, and missing controls become higher-volume errors at machine speed — misdiagnosed as hallucinations. Trust must be engineered through lifecycle governance, not bolted on after pilots. Automating dysfunction produces dysfunction at scale.
MISTAKE 5 PILOT PERMANENCE
Why you might be doing it: Pilots feel safe, controlled, and reversible — they demonstrate AI capability without committing to production risk.
Why it will cost you: Only 14% of CFOs report measurable ROI from AI. 95% of generative AI pilots fail to scale. Pilot permanence is not caution — it is the organizational pattern that keeps the 95% failure rate persistent. The 90-day mandate exists because pilots without production intent are not learning events. They are budget consumption events that erode credibility for the next initiative.
MISTAKE 6 TRUST AS AFTERTHOUGHT
Why you might be doing it: Ship the capability first, add governance later — reduces time-to-market and avoids slowing engineering.
Why it will cost you: Trust cannot be retrofitted into agentic systems without fundamentally re-architecting them. Agent identity, runtime governance, evidence trails, and provenance are architectural primitives — not features that can be added after deployment. Every production deployment without these creates trust debt that compounds at agent execution speed.
MISTAKE 7 SINGLE-MODEL DEPENDENCY
Why you might be doing it: Simplifies architecture, reduces integration complexity, single vendor relationship to manage.
Why it will cost you: Single-model strategies create unpredictable COGS, latency bottlenecks, governance risk, and single points of failure. Under outcome-based pricing, COGS volatility is a revenue risk, not just an operational inconvenience. Multi-model routing is not architectural complexity — it is the mechanism that makes SaS economics sustainable at scale.
7 FORCES THAT WILL SLOW YOU DOWN — AND HOW TO ROUTE AROUND THEM
These structural forces affect every Tier 2/3 SaaS company in this transition. You cannot eliminate them. Anticipate them and move faster than competitors who discover them by accident.
BLOCKER 1 THE TRUST DEBT WALL — DATA, MEANING, AND GOVERNANCE DEBT
The biggest counter-force in 2026–2028 is not model capability or infrastructure cost. It is trust debt: weak data quality, inconsistent semantics, unclear ownership, and missing controls accumulated over years of deferred governance investment. Agents do not fail gracefully — when meaning and governance are fragile, autonomy turns small defects into high-impact incidents at machine speed. Leaders cap autonomy after a few incidents. Legal and compliance blocks scaled deployment. Teams lose confidence and revert to manual workarounds. Fund trust debt paydown like platform work — not discretionary projects. The cost of a failed agentic deployment is not the pilot budget. It is the organizational credibility to attempt the next one.
BLOCKER 2 ONTOLOGICAL DEBT ACCUMULATION — SEMANTIC FRAGMENTATION AT AGENT SPEED
Ontological debt is the accumulated imprecision in how an enterprise defines its core domain objects across its technology stack. Unlike technical debt, which compounds slowly, ontological debt compounds at agent execution speed. One poorly-defined ‘contract’ object multiplied by 10,000 agent actions per day produces 10,000 semantically ambiguous decisions before anyone detects the pattern. Large enterprises average 600+ SaaS applications. Each has its own schema for core domain objects. When agents span these systems, semantic conflicts compound across every boundary. Organizations that do not treat ontology as a strategic program will find their agents increasingly constrained by semantic fragmentation.
BLOCKER 3 THE 95% PILOT FAILURE RATE — AMBITION DRAMATICALLY OUTRUNNING MEASUREMENT
Adobe’s 2026 AI and Digital Trends report finds that only 31% of organizations have implemented a measurement framework for agentic AI. MIT research documents that 95% of generative AI pilots fail to scale; only 14% of CFOs report measurable ROI. The pattern is consistent: ambitious deployment, insufficient instrumentation, inability to prove value, procurement skepticism, stalled expansion. The blocker is not capability — it is measurement rigor. Organizations that cannot instrument completion rate, reversal rate, escalation rate, and cost-per-outcome cannot defend their AI investments or direct them toward higher-value applications.
BLOCKER 4 THE TALENT STRUCTURAL GAP — NEW ROLES THAT DO NOT YET EXIST AT SCALE
Agentic systems require new structural roles — Context Engineers, Agent Designers, AgentOps Leads, Responsible AI Leads — that most organizations do not yet have at scale. These are not retraining targets for existing roles. They require new cross-functional skill sets spanning AI engineering, domain knowledge, governance, and outcome instrumentation. The talent supply chain for these roles is 18-24 months behind demand. Organizations that are not building internal academies, redefining career ladders, and recruiting for these roles now will face a capability constraint that is structurally harder to solve than any technology gap.
BLOCKER 5 DATA TOLL ECONOMICS — API CONNECTION FEES DESTROYING ROI MODELS
As AI agents require access to proprietary data across vendor systems, connection fees and API tolls are becoming the new cloud egress charges. Constellation Research identifies data tolls as potentially the biggest risk to scaling AI agents — larger than compute costs. The economics compound when multi-vendor agentic workflows require real-time data access across multiple systems. ISVs building outcome pricing models without instrumenting data access costs at the workflow level will find their models become insolvent as they scale. The legal battles between companies over data access are early signals of a structural cost dynamic that will reshape agentic platform economics.
BLOCKER 6 REGULATORY HEADWIND — COMPLIANCE COMPLEXITY GROWING FASTER THAN DEPLOYMENT READINESS
The EU AI Act, emerging state-level AI laws, sector-specific regulatory guidance for financial services, healthcare, and defense, and evolving international data governance frameworks are creating a compliance complexity that most enterprises are not yet equipped to navigate. The risk is not that regulation blocks deployment — it is that underprepared organizations deploy agents into regulated workflows, create compliance exposures, and trigger forced rollbacks that destroy organizational confidence in agentic AI. Organizations that build compliance-by-design into their agentic architecture — provenance, audit trails, risk classification, and human oversight gates — will deploy faster and more durably than those treating compliance as a deployment blocker.
BLOCKER 7 SHADOW AI PROLIFERATION — UNGOVERNED AGENTS CREATING INVISIBLE LIABILITY
75% of employees are expected to acquire, modify, or create technology without IT oversight by 2027. 15% of employees routinely use unsanctioned generative AI tools on corporate devices today. When the technology is agentic — capable of taking actions on behalf of the enterprise — shadow deployment creates invisible liability: ungoverned agents with no audit trails, no permission controls, no behavioral observability, and no accountability. The blocker is not shadow AI itself — it is the organizational response. Blanket bans drive shadow deployment underground; governance-light approaches create liability. The solution is sanctioned patterns: governed platforms, clear extensibility pathways, and organizational permission to experiment within defined guardrails.
YOUR 2026 QUARTERLY ACTION ROADMAP
Q1 builds what cannot be retrofitted. Q2 deploys with production governance. Q3 scales what is proven. Q4 establishes the position that defines 2027. Skip a quarter and the cost multiplies in the next.
Q1 2026 FOUNDATION
Build what cannot be retrofitted: trust architecture, measurement frameworks, and semantic foundations. Every architectural decision made in Q1 becomes the foundation on which scale is built or the constraint that prevents it.
What to Do This Quarter
• Conduct ontological audit of top 5 domain objects — the fragmentation you find is your most urgent trust debt
• Define and instrument the outcome measurement framework for your top 3 workflows before deploying any agents
• Extend IAM to agents as first-class principals — agent identity cannot be added after deployment without re-architecture
• Generate SBOMs for every build including model artefacts — supply chain visibility from day one
• Commission PQC exposure audit — classify all sensitive data by retention period and begin ML-KEM migration plan
• Declare ecosystem role: orchestrator, capability provider, or both — strategy differs radically for each
How to Know It Worked
• Ontological audit complete for top 5 domain objects
• Agent identity framework deployed for all new production agents
• SBOM coverage: 100% of new builds
• PQC exposure audit complete with migration roadmap
• Outcome measurement framework defined with baselines

Q2 2026 BUILD
Deploy the infrastructure that makes agentic delivery trustworthy: MCP servers, context layer, guardian agents, and behaviour regression suites. Q2 is the production commitment quarter — not pilots, not previews, but governed production systems.
What to Do This Quarter
• Publish production-grade MCP servers for top 5 capability surfaces (with SSO, RBAC, structured audit logs)
• Deploy Enterprise Context Layer with permissions-aware retrieval and freshness SLAs
• Implement guardian agents and policy-as-code for top 5 regulated workflows
• Build behaviour regression suites covering functional, policy-compliance, and adversarial scenarios
• Activate agentic RAG replacing traditional RAG for top 3 production workflows
• Launch FDIE bundling as standard commercial motion with first 3 enterprise reference deployments
How to Know It Worked
• MCP servers live for top 5 capabilities with enterprise governance
• Context Layer serving agents with >90% context quality score
• Guardian agents blocking policy violations in real time
• Behaviour regression suites covering >80% of intent specification space
• FDIE model in production with 3 reference customers

Q3 2026 SCALE
Expand the pattern to all major workflows, activate ecosystem plays, and achieve GCC 3.0 transformation. Q3 is the quarter where the architectural investments of Q1-Q2 compound — or where their absence becomes a constraint.
What to Do This Quarter
• Achieve Tier 0 autonomous resolution for top 10 support workflows with machine-legible APIs
• Activate multi-model routing (SLM + frontier + specialised) across all major workflows
• Deploy GCC factory lanes model with telemetry-led delivery and outcome pod structure
• Publish certified action sets (ACP + UCP) for top 5 commerce workflows
• Map proprietary schemas to FIBO/FHIR/Schema.org and publish open-source commodity schemas
• Launch A2UI for agent-generated interfaces in primary product surfaces
How to Know It Worked
• Tier 0 CX resolution rate: >60% for targeted workflows
• Multi-model COGS reduction: >30% vs single-model baseline
• GCC outcome attribution: 100% of engagements >$1M
• Certified actions live in ACP and UCP marketplaces
• Open-source schema published and referenced by 3+ ecosystem partners
Q4 2026 COMPOUND
Activate the Revenue Intelligence Layer, establish semantic authority, and build the compounding advantages that define 2027 competitive position. Q4 is about turning operational excellence into strategic position.
What to Do This Quarter
• Launch Revenue Intelligence Layer connecting every release to NRR, margin, and completion rate outcomes
• Establish semantic authority: domain ontologies referenced by at least 3 ecosystem partners as canonical
• Achieve quantum-safe cryptography for 40% of sensitive data systems
• Publish first annual Operational Trust Report with contractually committed trust metrics
• Complete GCC 3.0 transformation with all factory lanes operational and outcome-measured
• Define agent-to-agent dispute resolution protocol as machine customers begin scaling
How to Know It Worked
• Revenue Intelligence Layer: >70% of NRR variance explained by engineering release decisions
• Semantic authority: 3+ ecosystem partners referencing your domain schemas
• PQC migration: 40% of sensitive systems on ML-KEM
• Trust Report published with contractual commitments
• External agent invocation rate: >5% of total MCP surface invocations from non-owned agents
THE ONE-PAGE SUMMARY
Share this with your leadership team before your next planning session.
The situation
Salesforce, Dynamics 365, ServiceNow, and Workday have restructured commercial models around outcome units. Your buyers have seen this. They will demand it from you. The Tier 2/3 SaaS companies that redesign commercial architecture before the next renewal cycle will lead their category. Those that wait will follow someone else’s playbook.
Your strategic asset
Your domain data is your moat. Veeva owns clinical trial semantics. ServiceNow owns ITSM semantics. Blue Yonder owns supply chain semantics. Workday owns HCM workflow semantics. What domain objects, regulatory mappings, and workflow definitions do YOU own? That is your answer to MCP, A2A, and the orchestration platforms building on top of you.
The operational requirement
The 95% pilot failure rate is an operational problem, not a capability problem. Behaviour regression suites, AgentOps infrastructure, and the Revenue Intelligence Layer connecting engineering decisions to NRR outcomes are the foundations that convert pilots into scale. A 50-person Tier 2 engineering team with these foundations can outship a 500-person Tier 1 team without them.
Your 90-day action
Apply the 5-P Framework. Declare your ecosystem role. Define your outcome unit. Build your measurement baseline. Implement trust architecture. Publish your first domain schema. Then pick one business-critical workflow and rebuild it as a governed agentic system. Scale the pattern. Not the pilot.

Leave a Reply