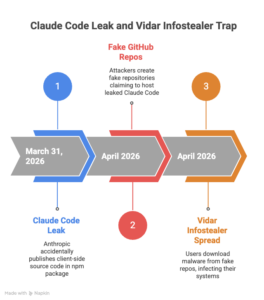
Claude Code Leak → Fake GitHub Repos → Vidar Infostealer: How the Trap Works

This is what happens all the time in modern security: a leak that gets a lot of attention happens, and attackers quickly turn it into a way to spread malware.
Threat actors are now taking advantage of the recent leak of the Claude Code source code by creating fake GitHub repositories that say they have the “leaked Claude Code” but actually send Vidar infostealer malware.
What really got out (and why it was important)
Claude Code is Anthropic’s AI agent that runs in the terminal and does coding tasks there. Because of this, it is naturally close to sensitive developer workflows. It is meant to run on its own, interact with the system, handle the LLM API, integrate with the MCP, and store data in memory.
On March 31, Anthropic accidentally made the tool’s client-side source code public by including a 59.8MB JavaScript sourcemap in the npm package that was published. According to reports, the leak included 513,000 lines of clear TypeScript spread across 1,906 files. These files revealed orchestration logic, permissions and execution paths, internal features, build details, and other security-related information.
It wasn’t surprising that the code was quickly downloaded and mirrored on GitHub, where it was forked thousands of times, making it easy for people to pretend to be someone else.
The attacker’s playbook: “curiosity + Google” as the way to get the word out
Zscaler says that threat actors used the leak as bait by making a malicious GitHub repository (published by a user named “idbzoomh”) that advertised a fake dump with claims like:
- “Unlocked business features”
- “No limits on use”
That’s the trick: promise access, get around restrictions, and take advantage of the fact that developers look first and check later.
The repo was optimized for search engines so that it showed up high in Google results for searches like “leaked Claude Code.” This isn’t advanced hacking; it’s just good operational discipline: make the bad repo easy to find, make it look trustworthy, and let organic traffic do the rest.
The payload chain
Users are asked to download a 7-Zip file with the Rust-based executable ClaudeCode_x64.exe inside.

When run:
- It drops Vidar, which steals information about goods (like credentials, browser data, crypto wallets, etc., depending on how it is set up),
- and it also installs GhostSocks, which is usually used as a proxy tool to send traffic and help keep access or hide command-and-control behavior.
Zscaler says that the archive is updated often, which is important because the delivery method is modular and can switch payloads over time, even if the current sample is “only Vidar.”
Researchers also found a second repo with almost the same code and layout, but its “Download ZIP” flow didn’t work during the analysis. This suggests that the same person is testing different ways to deliver the code.
The bigger picture (and why this keeps working)
GitHub is still a good place for malware to spread because people trust it by default and attackers are good at hiding payloads as:
PoC exploits, cracked tools, leaked source code, and “research” repositories.
In late 2025, we saw the same thing happen with fake PoCs that were aimed at inexperienced researchers. They took advantage of hype cycles and a sense of urgency.
What you can take away from this
High-interest events make high-conversion lures. That’s all you need to remember. An IP problem isn’t the only thing that can cause a leak. It turns into a way for malware to get into your computer.
What defenders should strengthen right away:
- Until you can be sure, treat “leaked repos” as hostile.
- Never run binaries from GitHub archives, especially droppers that look like “toolname_x64.exe.”
- Choose upstream packages that have been verified, signed releases, and builds that can be repeated.
- Keep an eye out for Vidar/GhostSocks signs, and make endpoint execution rules stricter for developer machines.

Leave a Reply